31
M
icrocontrollers
October 2015
ware algorithms with one that includes hardware security features
like hardware accelerated AES encryption, a true random number
generator and improved AES key storage.
The primary advantage of a hardware-accelerated AES block over
a software implementation is that hardware-accelerated AES is as
much as eight times faster than a software version. Two additional
advantages are power savings – a hardware AES takes fewer MCU
computations and therefore less power – and a smaller program code
size footprint. The same software AES encryption algorithms can run
more efficiently if they take advantage of the hardware-accelerated
AES built into a microcontroller. A true random number generator
(RNG) provides an improvement over a software implementation for
the creation of truly random keys. A true RNG uses physical phe-
nomenon – like noise – to create random numbers while software
implementations have to rely on an algorithm to create a random
number. A true RNG is less predictable than a software implemen-
tation providing more security. An additional security feature found
in some microcontrollers is the ability to store AES keys in memory
locations only readable from the hardware IP blocks. This way the
keys are no longer exposed to a software extraction.
Microcontrollers with additional security features combined with
software encryption algorithms can provide an excellent solution
when the embedded device is not physically accessible to hackers.
An example would be a thermostat in your house. You might worry
about somebody remotely accessing it to gain access to your internal
network. But you’re probably not worried about someone breaking
into your house to probe the microcontroller in your thermostat to
extract the AES keys out of it. If you have someone breaking into your
house, you have bigger problems than losing your AES keys. On the
other hand, if you have a smart meter outside your house, this might
be a more attractive target for hackers who want to physically attack
and steal the keys. Since the revenue stream for the electric company
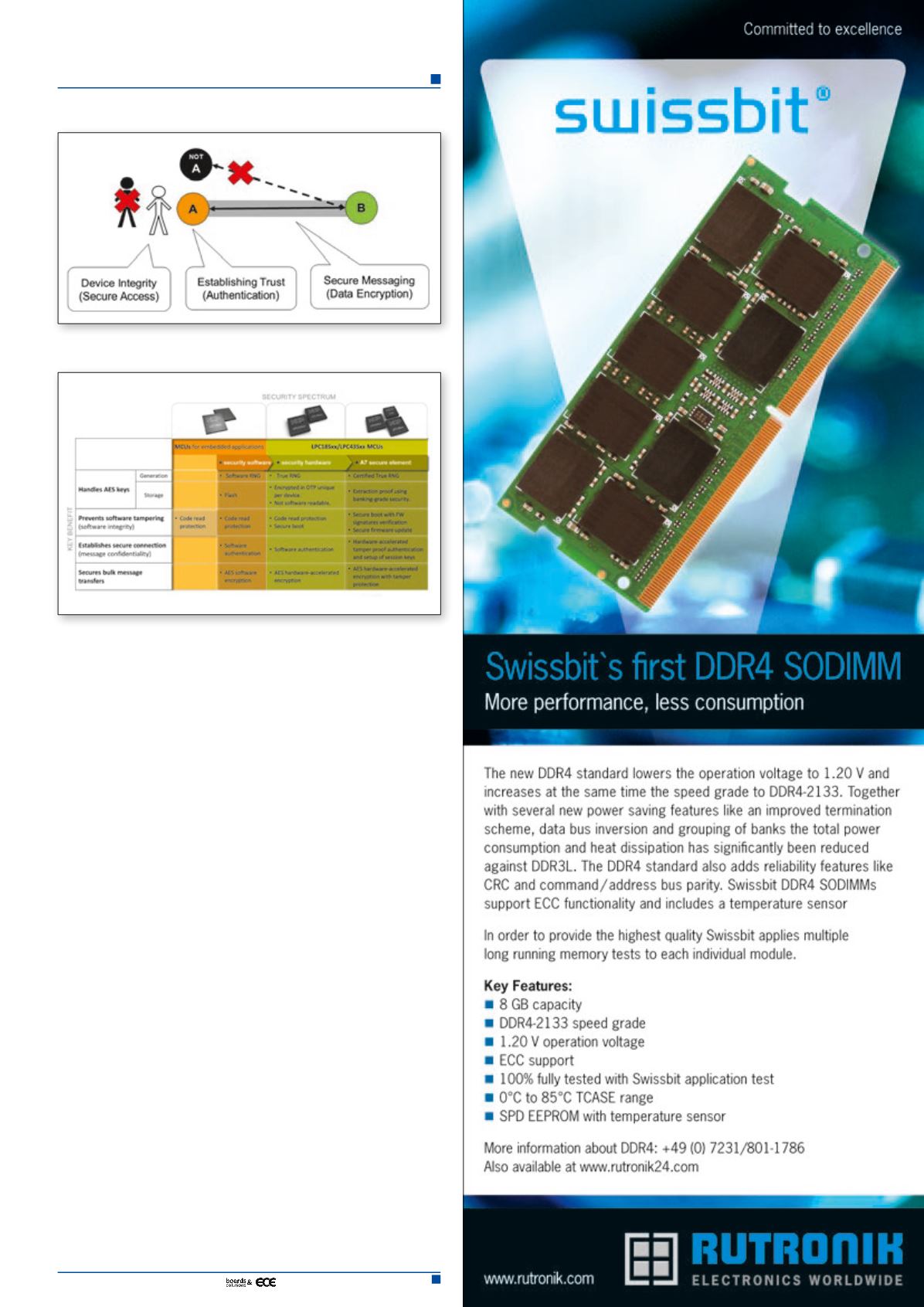
Figure 1. Security thought model
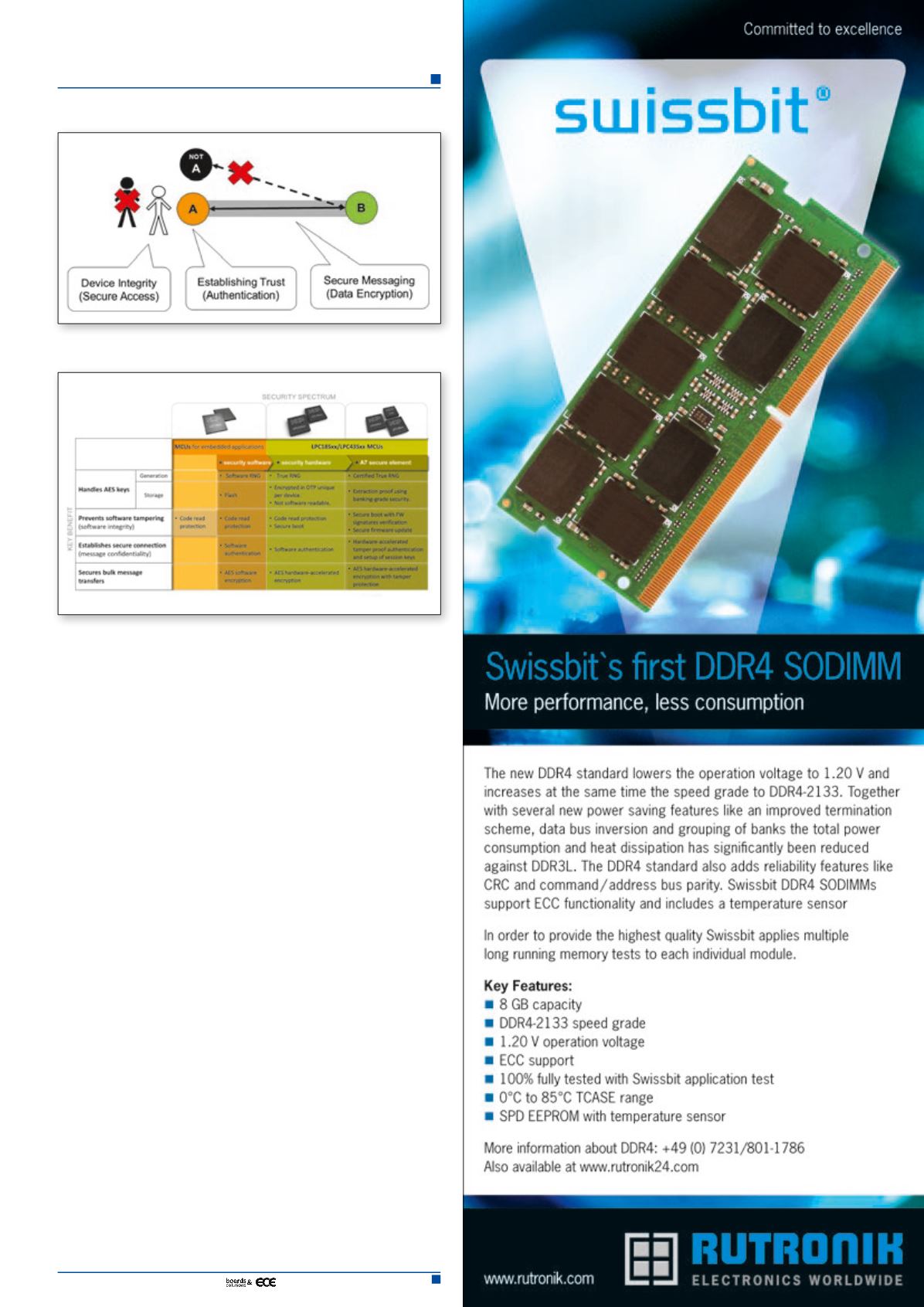
Figure 2. Spectrum of security