May 2016
16
I
nternet
-
of
-T
hings
Tamper protection: in order to avoid manipula-
tion or cyber-attacks, the application data and
program code is digitally signed. An anchor
of trust is the root public key, which must be
securely stored on the device. Digital signatures
are created using asymmetric cryptographic
means. First, the data or program code is
hashed (a hash function is a function that maps
data of any length to a character string of fixed
length. It is also collision-resistant, or a one-
way function or both. One example is SHA-
256.) Second, this hash value is asymmetrically
encrypted using the private key of the code
signer. The public key of this code signer key
is digitally signed by the root private key. The
result is called a certificate, which is attached to
the signature of the hash. By using these means,
a public key infrastructure can be set up to
allow different authorized parties to sign code
and data. RSA or ECC (Elliptic curve cryptog-
raphy) are established as forms of asymmetric
encryption. The IoT device itself can then val-
idate the signed data and program code. This
makes sure that the data and program code
have not been tampered with and that they
have been created by an authorized party.
Device identity: connected devices need to
be able to authenticate themselves. This can
be realized by using standard cryptographic
authentication schemes, which requires the
storage of a device private key in a way that can-
not be compromised. For authentication and
trusted communication, an open standard like
OPC UA is an excellent solution, as it enables
devices of different makes to be used in one
system with full interoperability. For imple-
menting the already-mentioned mechanisms,
specific care is required to achieve a complete
protection against the identified threats.
To achieve highest security for IP and tamper
protection, a high level of security is required.
Unlike the situation with software licensing in
the desktop PC area, where attackers are mostly
users trying to avoid license fees, the attackers
in this new field are often found in organized
crime, terrorism, secret services, or industrial
competition. What all of these attackers have in
common is that they have considerable finan-
cial resources for highly professional attacks.
Therefore, to inspire trust and confidence
in the user and safeguard the family jewels
of intellectual property of the makers, cryp-
tographic keys and calculations need to be pro-
duced in so-called secure elements. These can
be a Trusted PlatformModule, TPM, any other
solutions like TEE or Trustzone, or an industri-
al-grade dongle like CodeMeter that contains a
smart card chip with the highest security level,
certified according to Common Criteria. Using
any of the described secure elements makes it
possible to develop a truly secure IoT device.
The secure element will become an essential
small and isolated part of the device.
Flexible storage for multiple licenses: like
the apps on a smartphone, different data and
applications need to be licensed on an IoT
device. Either the secure element needs to be
capable of storing many cryptographic keys
and license options, like CodeMeter with its
large secure key storage of more than 300kB,
or external license files with the keys need
to be handled and loaded into the secure
element, as with TPM 2.0. To realize new
business models, this is definitely a must for
device makers, and it is not enough to store
single cryptographic keys.
Communication security: connected devices
need to be able to authenticate themselves and
guarantee privacy by encrypted communica-
tion and authenticity by digitally signed com-
munication. OPC UA is an excellent solution,
but the secure storage of private keys and the
execution of crypto algorithms in a secure and
efficient way are again key.
The industry-proven CodeMeter technology
made by Wibu-Systems is employed in sev-
eral widely used systems. It allows developers
an easy integration into their products and
processes and comes with the following com-
ponents.
Secure key storage is the heart of the tech-
nology, either with storage in an encrypted
and digitally signed file bound to an existing
secure element in an IoT device, or as hard-
ware with a smart card chip. The libraries allow
decryption and encryption (AES, ECC, RSA)
as well as the storing of flexible license models.
Figure 2. Examples of Wind River Embedded Development Kit including CodeMeter
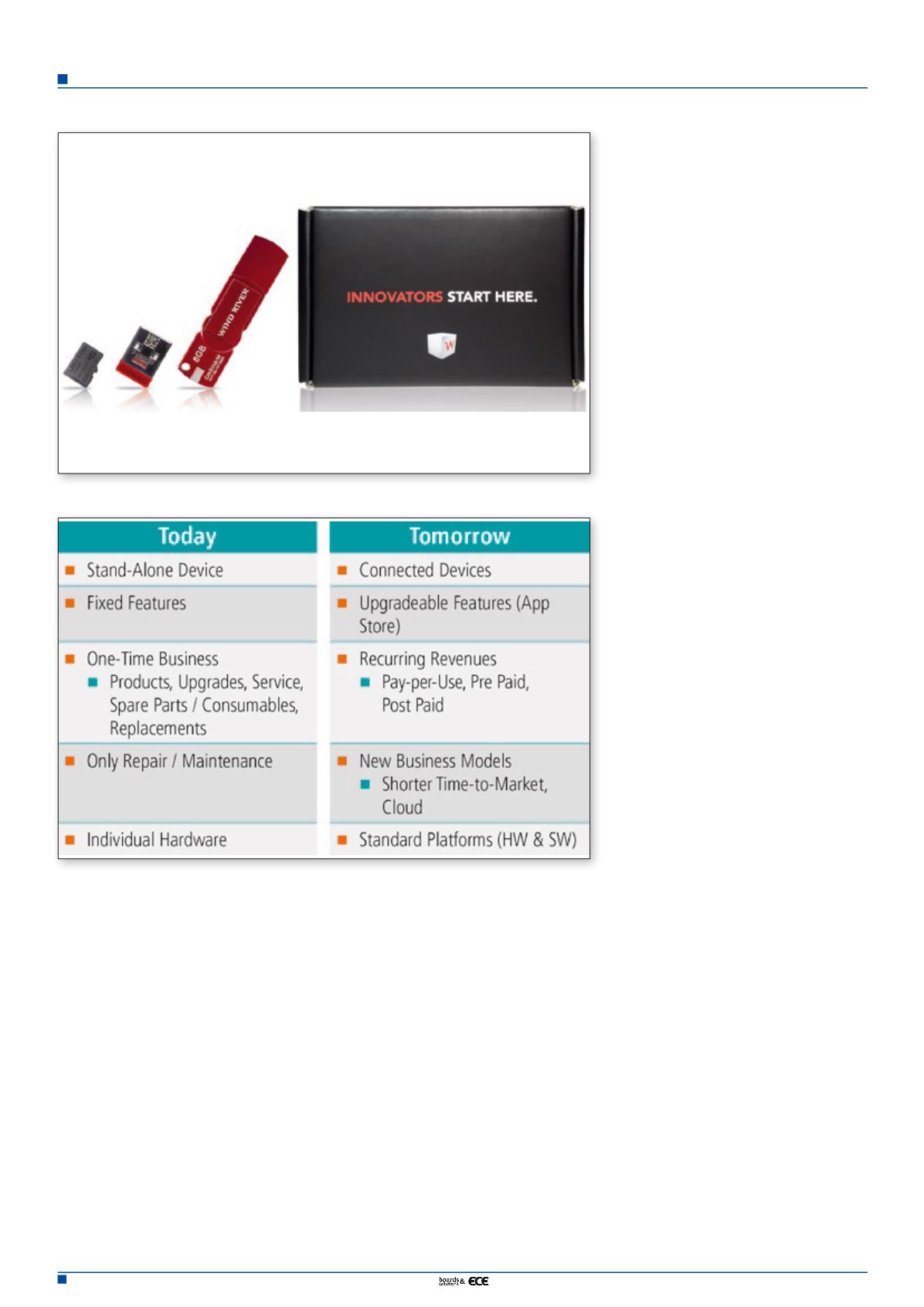
Table 1. Differences between current and future devices.