May 2016
12
I
nternet
-
of
-T
hings
importantly, also to shipping devices that con-
tain a hardware anchor with customer-specific
keys. These physical protection capabilities
can reduce costs particularly during installa-
tion and delivery processes.
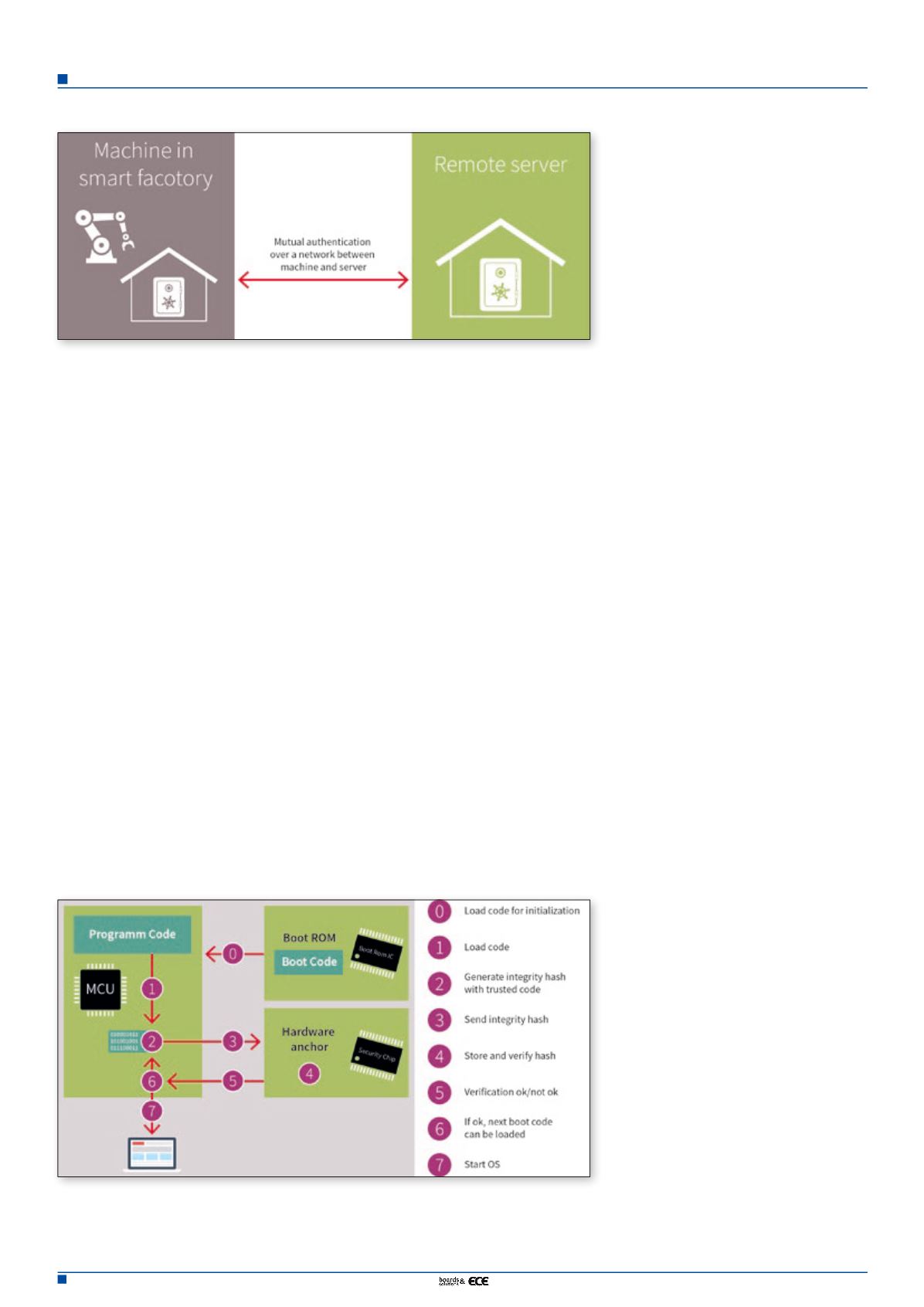
Mutual authentication refers to two parties
authenticating (securely identifying) each
other at the same time. In the context of smart
factories, this could be a server and a machine
authenticating each other before starting
a critical remote maintenance task such as
a firmware update or adaptation of critical
parameters. In this scenario, the secure iden-
tity stored in the machine hardware anchor is
verified by the server and vice-versa. The hard-
ware anchor contains the secret keys and offers
functionalities to verify the secured identities
of the other parties. It usually does this using a
public key infrastructure (PKI) scheme.
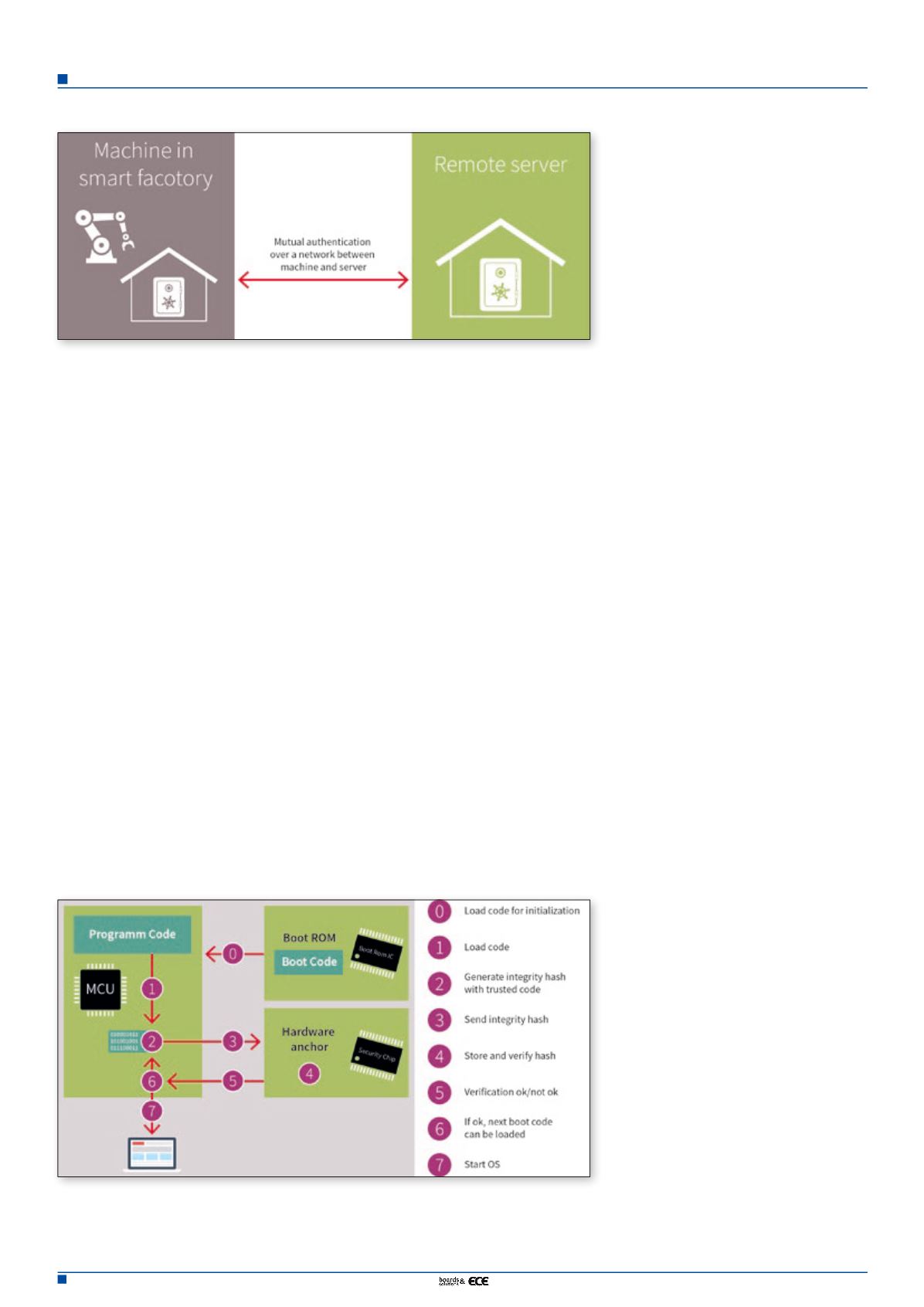
When an industrial automation system is set
up, the computing and controlling compo-
nents are equipped with a specific version of
the relevant software package. After this point
in time, the smart factory must be protected
against unintended changes to the software as
this could disrupt production, threaten plant
safety and enable know-how to be stolen. At
the same time, it must still be possible for soft-
ware to be updated intentionally, for example,
for maintenance purposes or to change cer-
tain features. Robust trust anchors also sup-
port this use case, for example by enabling a
secured boot process. The underlying con-
cept here is that code is only executed after its
integrity has been verified in advance by the
hardware anchor.
By using state-of-the-art microcontrollers
and stand-alone security controllers such as
the OPTIGA product family it is possible to
implement a hardware-based trust anchor
that protects the system software against
attacks. The key to successful protection lies
in the use of open industry standards that
allow seamless connectivity across existing
and new systems.
For many manufacturers, protecting their
products against counterfeit is a top prior-
ity. With its OPTIGA Trust product family,
Infineon offers a complete security solution
comprising a chip and software for electronic
accessories. The chip is based on asymmetric
cryptography and is easily integrated into elec-
tronic accessories thanks to its compact pack-
age (2 mm x 3 mm) and turnkey set-up. In
order to check whether or not a part is genuine,
the host system sends a challenge (essentially a
random number) to the chip in the accessory.
The OPTIGA Trust subsequently generates a
response using the chip-individual key. If suc-
cessfully authenticated by the chip, the acces-
sory or replacement part is accepted by the
system and can be used without restrictions.
Following the same principle, the OPTIGA
Trust E was specifically developed for protec-
tion of high-value goods in industrial applica-
tions. It features an I2C interface as well as an
extended temperature range (-40 to +85 °C).
This would be of benefit to manufacturers of
wind turbines, for example, who would want
to avoid damage to the overall system caused
by counterfeit replacement parts. Both the
OPTIGA Trust and the OPTIGA Trust E are
delivered with code to simplify integration of
the chip into spare parts.
Preventing counterfeit through authentica-
tion is just the first step in the process of safe-
guarding the overall system. Further security
functions are necessary to protect applica-
tion-specific information (e.g. customer data
and intellectual property) and the overall
operating procedure. The OPTIGA Trust P
security solution comes as a security controller
with a Java Card operating system and can be
flexibly programmed for a wide range of appli-
cations. This in turn allows the applications to
be managed in the field as OPTIGA Trust P
supports a Global Platform specification.
The OPTIGA TPM (Trusted Platform Mod-
ule) portfolio covers the broadest range of
security requirements. These security control-
lers are based on the international standard of
the Trusted Computing Group, an association
of leading manufacturers from the IT indus-
try. TPMs have already successfully proven
themselves in computer applications, and this
technology is now making its way into new
networked systems and devices such as rout-
ers, industrial facilities and cars.
The members of the OPTIGA TPM family
have been validated and security-certified
according to the Common Criteria certifica-
tion process. To permit easy integration into
a system, the OPTIGA TPM family supports
commercial and open source code for Win-
dows and Linux, including derivatives and
Infineon tools. The OPTIGA TPM family
comprises a broad range of security control-
lers complying with the standards TPM 1.2
and TPM 2.0, which, depending on the appli-
cation area, are available for various tempera-
ture ranges and offer different interfaces such
as SPI,I2C and LPC.
One area where OPTIGA TPMs can be used
in industrial applications is secured data
transmission or storage. In such an appli-
cation, the key factor is the combination of
Figure 3. A secure boot process ensures platform integrity of computing and control systems in
industrial environments.
Figure 2. Mutual authentication of machines over a network