October 2015
19
T
ools
& S
oftware
In contrast to existing security products that
only scan for attacks which have already hap-
pened, emSecure seeks to implement security
during the design process of the product, pre-
cluding such attacks. The aim is to prevent the
intrusion of manipulated firmware by third
parties. For this purpose, the manufacturer
generates a key pair and couples the public
key in the bootloader of the product where
firmware updates are managed.
Any firmware update is signed with the pri-
vate key. In order to do so, first a hash value is
calculated for the firmware by using a secure
hash algorithm (SHA1). The hash is then
padded – which prevents common mathe-
matical attacks – and encrypted by RSA. It is
important to mention that the firmware is not
encrypted. Signature verification can be done
in-product or off-product. With in-product
verification the firmware for example verifies
the digital signature at boot-time and refuses
to run when the signature cannot be veri-
fied. With off-product verification an external
application, e.g. a PC application communi-
cating with the device, reads the signature and
data from the product and verifies it.
The necessary key pair can be generated in
two different ways, either by random seed
or by help of a passphrase. The latter has the
advantage that keys can be regenerated. This
allows to not store the private key, but gen-
erate it only when it is needed. However, the
passphrase should not be too obvious, like the
name of the company. The passphrase has to
be kept separate and secure, just like the pri-
vate key. For IoT devices, such anti-hacking
protection is essential. They can be small, but
still secure, as emSecure offers higher perfor-
mance on the back of low resource consump-
tion. As a pure software-based solution, it is
also affordable and can easily be integrated
into existing products, too.
The second area of application is anti-cloning.
Cloned devices and applications are a grow-
ing risk, not just for turnover and reputation
of the affected manufacturers. They can also
be dangerous for the user and often have
limited functionality and lifespan. Accord-
ing to official estimates, one in ten electronic
devices contain illegal parts, be it copies or
illegally recycled ones. With emSecure, pro-
tection against cloning can be integrated into
the original device. First a key pair is gener-
ated at a secure facility. The private key will
be included in the production process of the
product. At the end of the production process,
after the unit is assembled and tested, some
hardware-specific, fixed, and unique data, like
the unique ID of the microcontroller is read
from the unit. This data is signed by emSe-
cure with the private key and the signature is
written back to the unit into an OTP area or a
specified location on memory.
The public key will be included in the firm-
ware which will run on the product. When
the firmware is running it will read the unique
data from the unit and verify it with the sig-
nature. When the signature does not match,
for example when it was simply copied to a
counterfeit unit with other unique data, the
firmware will refuse to run. This means the
firmware cannot simply be read out and cop-
ied into the cloned hardware. Hackers might
eventually deactivate the clone check, if pro-
vided with enough time and budget. However,
the clone will then be uncovered with the first
authentic firmware update, as it again con-
tains verification functions and will identify
the clone.
Segger uses emSecure for its own products.
The latest version of its J-Link debug probe
features both anti-hacking and anti-cloning,
while the new IDE Segger Embedded Stu-
dio uses it for authenticating licenses. emSe-
cure aims for portability and is designed to
fit speed and size requirements for different
targets. By default it uses 2048-bit keys, which
are considered unbreakable in the near fore-
seeable future and can be created from prov-
able primes. The process of verifying data is
technically split up into two steps, hash com-
putation and signature decryption and com-
parison of hash values. Performance tests on
an STM32 Cortex-M4 microcontroller, run-
ning at 200MHz, have shown that verification
for the standard 2k-bit keys take less than
32ms. Static RAM requirement is zero, as ver-
ification takes place on the stack.
emSecure comes as a package with all neces-
sary applications for the generation and ver-
ification of digital signatures, including the
source code. This way, the user can keep full
control of the code used in his product. The
package also contains Sign & Verify, a Win-
dows tool for easy drag-and-drop creation
of digital signatures and the verification of
signed files. Sign & Verify brings security to
any kind of data transmission, be it commer-
cial or private use. A pair of public and private
keys is used to create and verify digital signa-
tures. Digital documents can be signed with
the private key.
Signing data this way is very helpful even in
the private area. Modifications of the data
during transmission – be it through a virus, a
trojan or any willful manipulation – will no
longer go unnoticed. The utility can also be
used commercially, for example to make sure
that data stored to and recalled from a server
is unchanged. The Sign & Verify package con-
tains a key pair for evaluation purposes. For
private use, a unique key pair is available from
Segger for free, on request. For commercial
use, both the key generator and the source
code are available, a license is required.
n
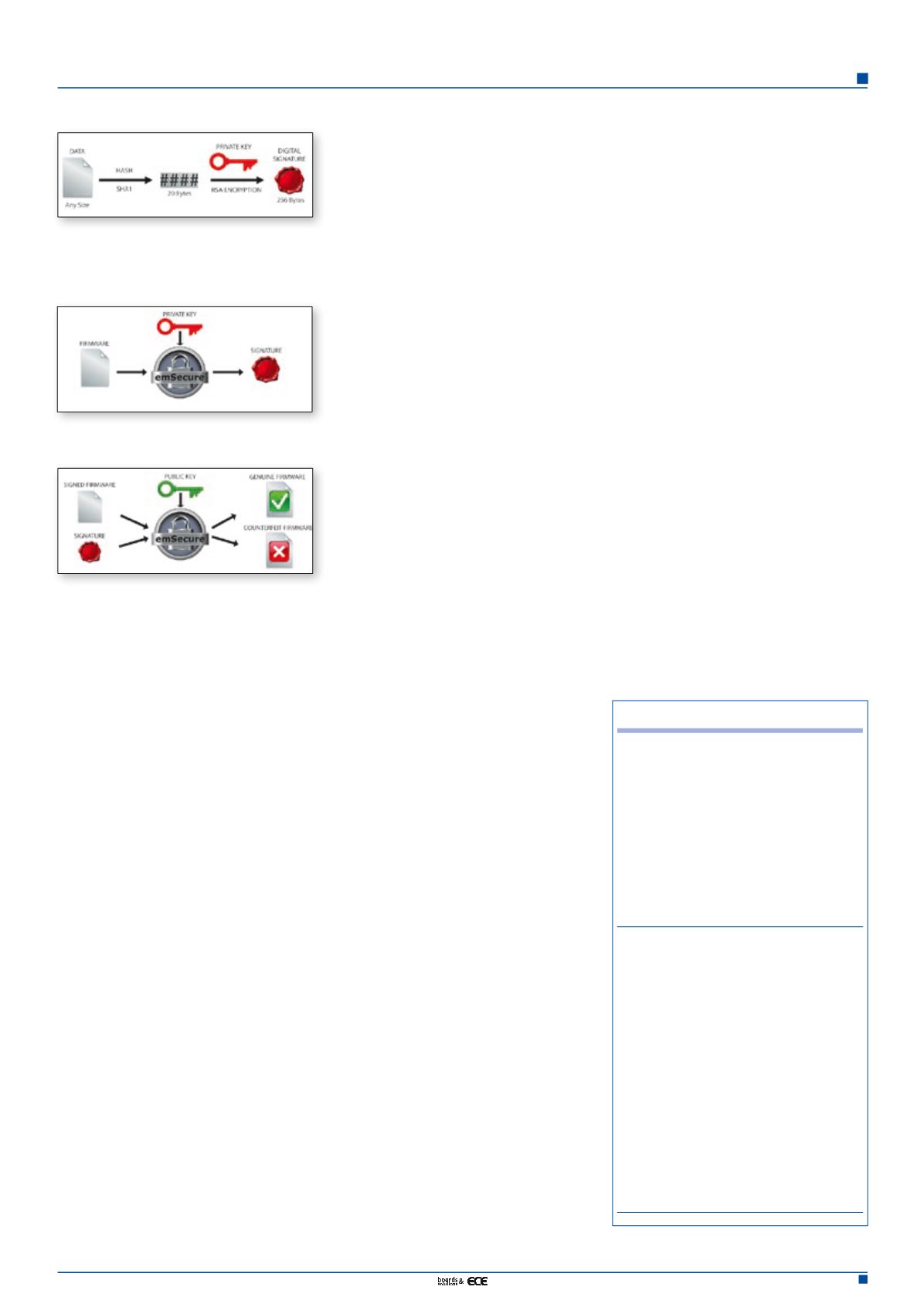
Figure 1. Generation of a signature for the
data to send a hash value. This hash value is
encrypted by RSA key. The data itself is not
encrypted.
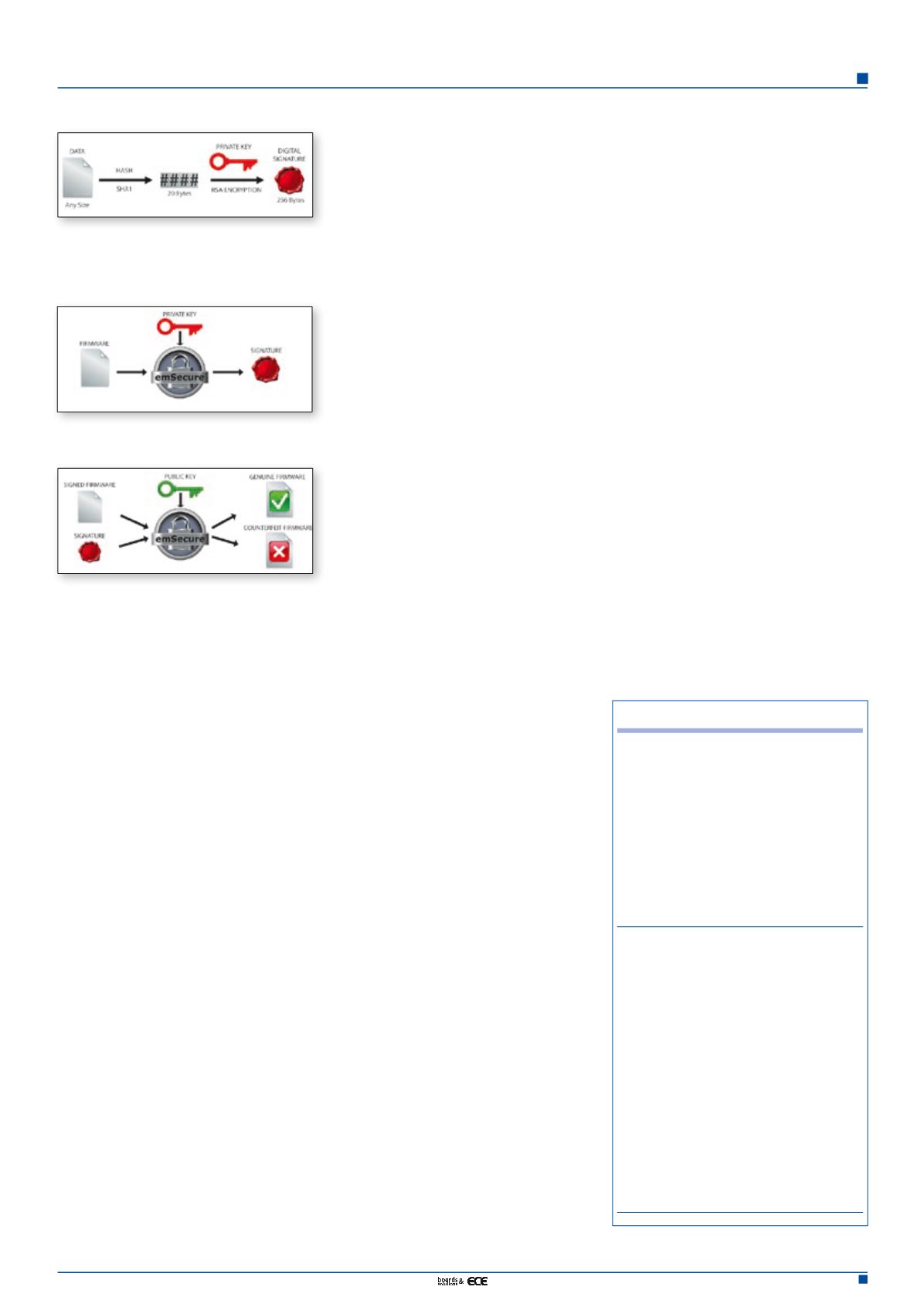
Figure 2. Firmware update is signed by means
of the private key.
Figure 3. Verification of signed firmware at
the recipient by mean of the public key.
Product News
Wind River at IOT Solutions
World Congress in Barcelona
Wind River has announced its participation
at IOT Solutions World Congress taking
place in Barcelona on 16 – 18th Septem-
ber. Together with parent company Intel,
Wind River will be exhibiting a range of IoT
product demonstrations including real-life
implementations within a smart city.
Vector Informatik announces
Technology Days 2015
On 28 and 29 October 2015, the Vector
Technology Days will have their premiere at
the Motorworld in Böblingen, Germany. In
a fittingly automotive ambience with 1000
m² of floor space, the high-tech company
will present forward-looking technologies
that you can touch. Vector is opening up its
development labs and will demonstrate the
latest product developments. The exhibition
will be flanked by a forum featuring short
talks on current development topics, work-
shops on all aspects of Vector’s core compe-
tency, and basic seminars.